Btrieve/Pervasive record manager engines have been the data interface backbone of choice for both Advanced Accounting (and earlier "Books") as well as versions of the TAS 4GL integrated development environment since the late 1980's. A number of other accounting software and multi-user database systems also continue to rely on the speed and robustness provided by these engines, a key feature of which has been expandability and true client-server support.
Version 11 was released in September of 2010 and remains in widespread use.
Important note: Pervasive v12 will no longer support XP Pro nor Windows 2003 Server.
Actian now owns Pervasive and here is their product availability notice:
FAQ's:
Download page:
http://www.pervasive.com/database/Home/Products/PSQLv12.aspx
Hardware requirements are the same for both versions 11 and 12.
It is expected that product support and updates for version 11 will continue until June 30, 2015.
There is currently no rush for existing users to migrate to version 12. It will primarily be of interest for new users, users who are on older versions and especially pre-v10 systems who will now likely want to migrate to v12 rather than v11, and users who need to expand their license counts.
One feature of the new version is an interesting defragmenter that can be run while the files are open (see screen shot at end).
Other currently outlined features may be of little to no benefit for existing v11 users.
First look:
As an initial test, we installed the workgroup engine on a desktop Windows 7 PC (32-bit O/S, SP1) and also on an ASUS Transformer Book running Windows 8.1 (32-bit version). Both installations went very smoothly, and with no issues. The workgroup engine can be installed as an application or as a service. Most users will want to install as a service. We installed one as a service, and one as an application.
In both cases (and has been our experience with essentially all prior Pervasive installations since version 7), both PC's had to be re-booted before our test applications would run (the installation does not tell the end user however that a re-boot is necessary, but this is something we have routinely advised). After re-booting and after some initial testing with two completely different applications running on each of the PC's, they both appear to be working exactly as expected and as they have with prior versions of Pervasive/Btrieve.
On one of the test PC's, we noticed something different than in the past: the presence of an older Btrieve 6.15 engine in the application folder did not create a problem with the Pervasive 12 engine running. And in fact, we were able to run one application using Pervasive v12 and another application using Btrieve 6.15 at the same time. This previously has not been possible.
The installation default group now is Actian PSQL 12 rather than Pervasive.
Installed Pervasive tools such as the License Administrator, Gateway Locator and Rebuild look substantially similar as does the Pervasive Control Center (PCC). User data files will not have to be rebuilt, and the "highest" Pervasive internal file format remains at 9.5 as it has since the Pervasive 9.x series.
Unfortunately Pervasive v12 continues to by default enable limiting data file sizes to 2GB before they "segment" which was a limitation imposed by Windows NT but which has not been an issue in newer Windows operating systems. Segmented data files cause various potential problems including how multi-company file naming extensions are deployed within TAS-based systems as well as can create potential backup, data integrity, reindex, manual file deletion/renaming and other file handling issues, and therefore is not supported. Pervasive users will need to uncheck this option so that segmentation never occurs (and this needs to be done in the event of a re-installation as well).
And, all supported protocols continue to be enabled by default in version 12. Most users only need TCP/IP and non-used protocols should be removed by unchecking them (see below).
Some final random thoughts:
We would be hopeful that the addition of the defragmenter feature might also mean that status code 46 problems resulting from access of the files from outside of Pervasive's handling might also be reduced or eliminated, but we suspect it will not. The defragmenter however may prove to be a very useful diagnostics and general analysis tool.
With server version purchases, Actian is offering for free (but as a separate download) its "Actian Analytics Platform for PSQL." This in part shows the influence of the new product owner and future directions that the product might take. This tool looks interesting as well, but is not something we have yet looked at.
The installer update which automatically detects the bitness of client operating systems could backfire if installation and connectivity problems related to the 64-bit Pervasive client engine continues to occur with 64-bit client operating systems. With v11, users have had more success installing 32-bit clients on client-server systems even if the server install was 64-bit and even though the clients are running 64-bit operating systems. If this remains the case and there is no way to install 32-bit components on a 64-bit PC, then this will be a potential problem.
The legacy 32-bit Btrieve 6.15 continues to work for older users who already had this engine on even Windows 8 systems (32-bit and 64-bit). Compatibility issues with this old version (despite its limitations, and despite not having been officially supported by Pervasive since the late 1990's) remains far fewer than with any subsequent version. And contrary to what might have been published elsewhere, it does run on 64-bit Windows 7 or Windows 8. It is not however suited for more than a relatively few simultaneous uses and does not provide client-server support, and it requires higher local user privileges than the newer engine. Its tiny footprint and its ability to "keep on ticking" however is quite admirable.
In any event, it appears that Pervasive v12 should be a smooth migration for prior Pervasive users; and for new users, preliminary indications are that it is a solid product.
Hardware requirements are the same for both versions 11 and 12.
It is expected that product support and updates for version 11 will continue until June 30, 2015.
There is currently no rush for existing users to migrate to version 12. It will primarily be of interest for new users, users who are on older versions and especially pre-v10 systems who will now likely want to migrate to v12 rather than v11, and users who need to expand their license counts.
One feature of the new version is an interesting defragmenter that can be run while the files are open (see screen shot at end).
Other currently outlined features may be of little to no benefit for existing v11 users.
First look:
As an initial test, we installed the workgroup engine on a desktop Windows 7 PC (32-bit O/S, SP1) and also on an ASUS Transformer Book running Windows 8.1 (32-bit version). Both installations went very smoothly, and with no issues. The workgroup engine can be installed as an application or as a service. Most users will want to install as a service. We installed one as a service, and one as an application.
In both cases (and has been our experience with essentially all prior Pervasive installations since version 7), both PC's had to be re-booted before our test applications would run (the installation does not tell the end user however that a re-boot is necessary, but this is something we have routinely advised). After re-booting and after some initial testing with two completely different applications running on each of the PC's, they both appear to be working exactly as expected and as they have with prior versions of Pervasive/Btrieve.
On one of the test PC's, we noticed something different than in the past: the presence of an older Btrieve 6.15 engine in the application folder did not create a problem with the Pervasive 12 engine running. And in fact, we were able to run one application using Pervasive v12 and another application using Btrieve 6.15 at the same time. This previously has not been possible.
The installation default group now is Actian PSQL 12 rather than Pervasive.
Installed Pervasive tools such as the License Administrator, Gateway Locator and Rebuild look substantially similar as does the Pervasive Control Center (PCC). User data files will not have to be rebuilt, and the "highest" Pervasive internal file format remains at 9.5 as it has since the Pervasive 9.x series.
Unfortunately Pervasive v12 continues to by default enable limiting data file sizes to 2GB before they "segment" which was a limitation imposed by Windows NT but which has not been an issue in newer Windows operating systems. Segmented data files cause various potential problems including how multi-company file naming extensions are deployed within TAS-based systems as well as can create potential backup, data integrity, reindex, manual file deletion/renaming and other file handling issues, and therefore is not supported. Pervasive users will need to uncheck this option so that segmentation never occurs (and this needs to be done in the event of a re-installation as well).
And, all supported protocols continue to be enabled by default in version 12. Most users only need TCP/IP and non-used protocols should be removed by unchecking them (see below).
Pervasive v12 - removed unneeded communication protocols
(same as in prior versions)
Some final random thoughts:
We would be hopeful that the addition of the defragmenter feature might also mean that status code 46 problems resulting from access of the files from outside of Pervasive's handling might also be reduced or eliminated, but we suspect it will not. The defragmenter however may prove to be a very useful diagnostics and general analysis tool.
With server version purchases, Actian is offering for free (but as a separate download) its "Actian Analytics Platform for PSQL." This in part shows the influence of the new product owner and future directions that the product might take. This tool looks interesting as well, but is not something we have yet looked at.
The installer update which automatically detects the bitness of client operating systems could backfire if installation and connectivity problems related to the 64-bit Pervasive client engine continues to occur with 64-bit client operating systems. With v11, users have had more success installing 32-bit clients on client-server systems even if the server install was 64-bit and even though the clients are running 64-bit operating systems. If this remains the case and there is no way to install 32-bit components on a 64-bit PC, then this will be a potential problem.
The legacy 32-bit Btrieve 6.15 continues to work for older users who already had this engine on even Windows 8 systems (32-bit and 64-bit). Compatibility issues with this old version (despite its limitations, and despite not having been officially supported by Pervasive since the late 1990's) remains far fewer than with any subsequent version. And contrary to what might have been published elsewhere, it does run on 64-bit Windows 7 or Windows 8. It is not however suited for more than a relatively few simultaneous uses and does not provide client-server support, and it requires higher local user privileges than the newer engine. Its tiny footprint and its ability to "keep on ticking" however is quite admirable.
In any event, it appears that Pervasive v12 should be a smooth migration for prior Pervasive users; and for new users, preliminary indications are that it is a solid product.
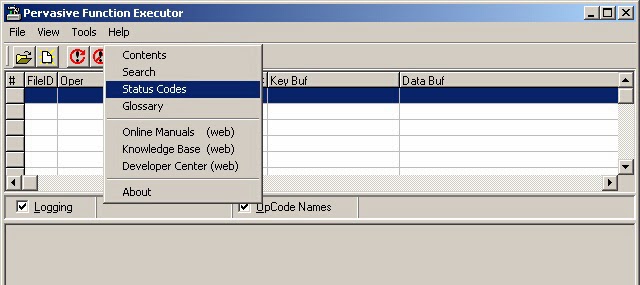
New PSQL12 Defragmenter tool